 SIRDA - Security Incident Response and Data Aquisition (32499 downloads )
– 7b06efbcb86edfe3ba026f1e47aa5c532566b364
SIRDA - Security Incident Response and Data Aquisition (32499 downloads )
– 7b06efbcb86edfe3ba026f1e47aa5c532566b364
When I was first studying for my CISSP back in 2017 I became obsessed with Data Acquisition during an incident response, and although I searched for weeks, I could find no product that would allow me to collect all the data I needed, at least not without spending thousands of dollars. I did find bits and pieces of code around the Internet that gave me great ideas to start with but still I couldn’t find a good centralized application that would bring it all together and also be easy to use for anyone. So instead I decided to start putting together my own incident response application, hence SIRDA was born.
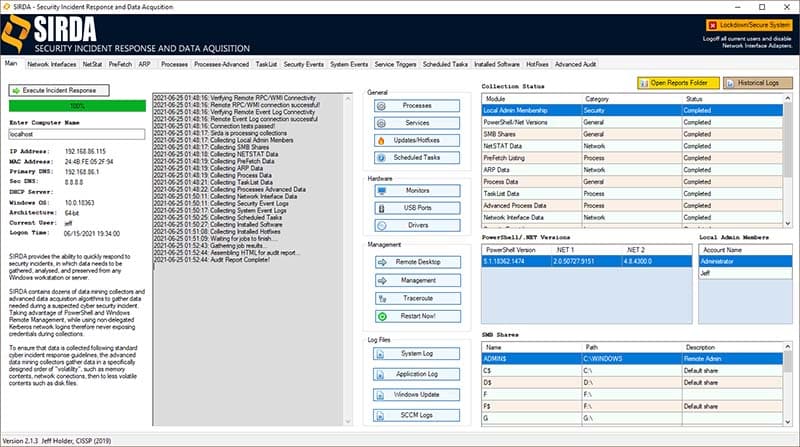
SIRDA provides the ability to quickly respond to security incidents, in which data needs to be gathered, analyzed, and preserved from any Windows workstation or server.
SIRDA contains dozens of data mining collectors and advanced data acquisition algorithms to gather data needed during a suspected cyber security incident. Taking advantage of PowerShell and Windows Remote Management, while using non-delegated Kerberos network logins therefore never exposing credentials during collections.
To ensure that data is collected following standard cyber incident response guidelines, the advanced data mining collectors gather data in a specifically designed order of “volatility”, such as memory contents, network connections, then to less volatile contents such as disk files.
This is one of the first of its kind applications that is geared directly towards incident response, it can be ran locally on the host computer or can be use for remote systems. If you want to run it locally, in the computer name just type “localhost”, or for remote you should use the FQDN of the remote system.
All the data is exported into 17 excel spreadsheets, each representing one of the tabs you see on the main console. It also contains an Advanced Audit html file, which contains even more detailed logging and analysis of the target system.
This is an ongoing project and will grow over time with the amounts and types of data collected as needed to complete a robust and highly useful tool for all Incident Response Teams.
Several people have asked me in the past would I release the code that went into the application, and yes even though I understand their concerns about it being a security type application and they want to see all the hundreds of thousands of lines of code in it. It’s no different that any application developer not releasing the actual internal code, so no I do not release code, if that goes against what you believe then don’t use it.
SIRDA - Security Incident Response and Data Aquisition (32499 downloads ) – 7b06efbcb86edfe3ba026f1e47aa5c532566b364















COMMENTS